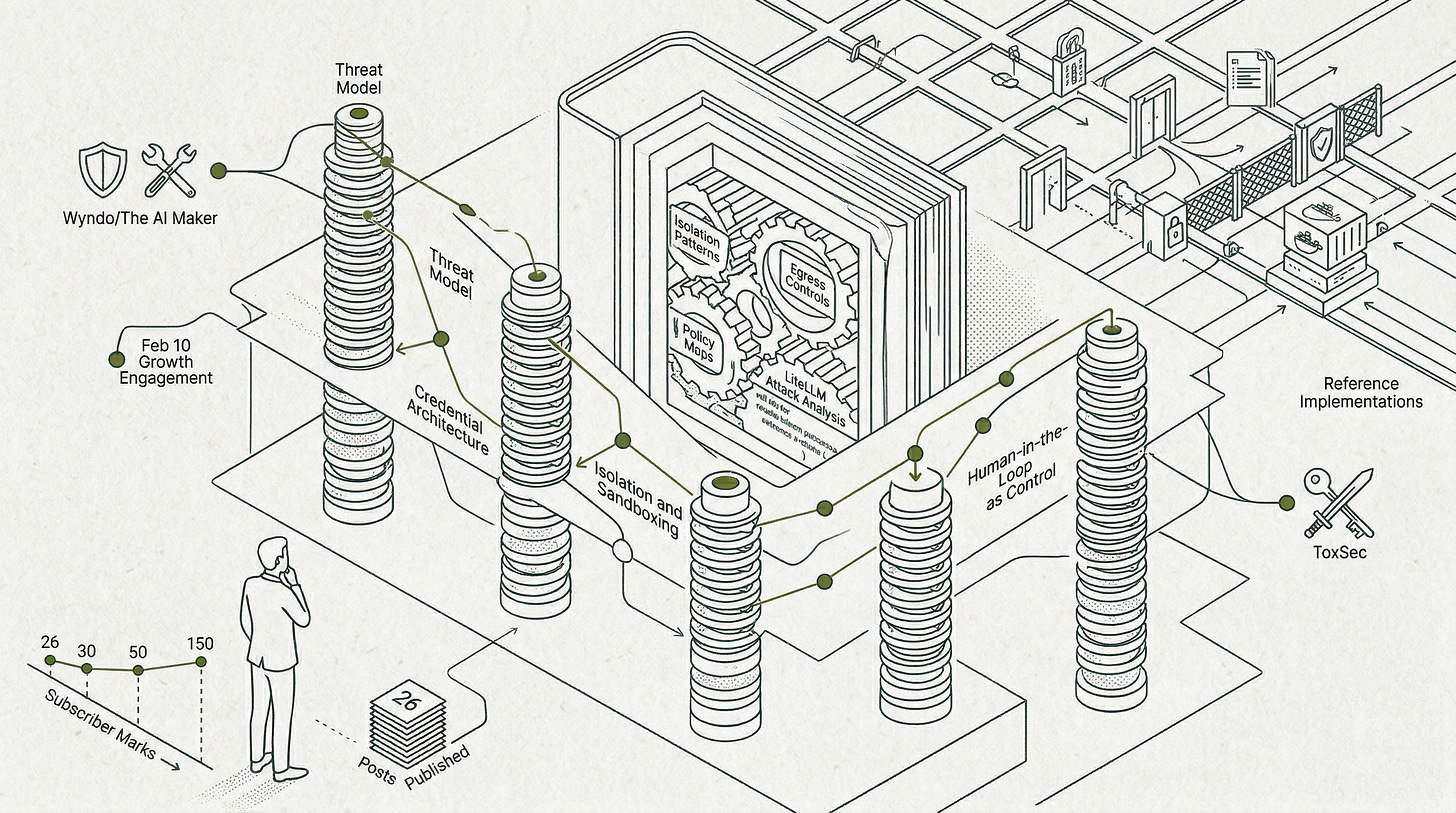
150 Subscribers, One Quarter, and the Book That Got Out of Hand
A deep dive into the first quarter of 2026. Reviewing growth, successful collaborations, and the upcoming Agentic AI Security Stack guide that became a book.
Let me start with the number: 150.
Three months ago, this newsletter had 26 subscribers. Most of them were people I had personally told about it. The list was short enough that I could have named every single person on it. Today it stands at 150, and I genuinely do not know most of you, which is the best possible outcome a writer at this stage can hope for.
This post is my attempt to account for Q1 2026 honestly: what got written, what resonated, what didn't, and, most importantly, the two people who made the growth inflection actually happen. It also has an update on the Agentic AI Security Stack, and if you have been waiting on that promise since February, you will want to read to the end.
The Quarter in Numbers
Between January 6 and March 31, I published 26 posts. That is approximately two per week, across a range from short tactical pieces to deep-architecture breakdowns. Total views across those 26 posts came to over 5,800. Open rates on email distributions averaged around 33%, which is healthy for a technical newsletter at this stage.
The posts that landed hardest, measured by views:
OpenClaw Hardened Deployment: A Non-Technical Companion Guide (Feb 10): 1,415 views, 17 signups, 16 shares
The Secret That Shouldn’t Exist (Jan 20): 633 views, 6 shares
Stop using OpenClaw / MoltBot / ClawdBot until you read this (Jan 28): 328 views, 7 signups, 6 shares
The threat landscape for Agentic AI (Jan 13): 250 views, 5 reactions
Those four posts alone account for roughly 45% of total Q1 views. The pattern is worth noting: all four of them were either tied to a collaboration or were the kind of “I need to warn you about something” writing that readers share. Pure technical explainers get consistent engagement. Urgent, specific, opinionated pieces get shared.
January: Building the Foundation
January was largely about turning the corner from broad AI fluency content into something with a tighter security focus. The first few posts of the year (”Why everything I’ve written is actually related to security“, “The Manager Layer“, “The Threat Model for Agentic AI“) were me drawing the explicit through-line that had been implicit in earlier work.
The standout moment of January wasn’t the most-viewed post. It was “The Secret That Shouldn’t Exist,” which explored how modern agents get API access without carrying keys. It pulled 633 views with only 29 subscribers on the list at the time. That told me the organic discovery potential was real if I kept publishing consistently on the right topics.
The OpenClaw post a week later (328 views, 8 reactions) confirmed the same thing from a different angle. Writing that is specific, urgent, and opinionated travels faster than writing that is comprehensive but safe.
February: The Wyndo Collaboration
This is the most important thing I can tell you about Q1.
On February 10, a post titled “OpenClaw Hardened Deployment: A Non-Technical Companion Guide“ hit 1,415 views in a single publication cycle. It drove 17 signups, 16 shares, and 6 reactions. It is, by a significant margin, the highest-performing piece this newsletter has ever published.
That did not happen because I wrote something brilliant. It happened because I reached out to Wyndo from The AI Maker with a collaboration idea, and he said yes. That might sound simple, but it isn’t. Wyndo had no obligation to give a newsletter with 30-something subscribers the time of day. He engaged with the idea seriously, shaped it into something better than what I had pitched, and delivered his side with the quality his audience expects. That generosity is what moved the needle.
The setup: Wyndo published a security hardening guide for OpenClaw on his side (you can read it here). I published the technical companion covering hardened deployment with Ansible (here is my side). Two pieces, one shared topic, cross-linked.
The result was the single-day growth event that pushed this newsletter from the mid-thirties into the fifties, and the momentum carried through February. If you subscribed anywhere in February and are reading this, there is a good chance Wyndo’s audience is what made you land here.
If you are not subscribed to The AI Maker, I would strongly recommend fixing that. Wyndo’s work is practical, technically rigorous, and covers the operational side of AI tooling in ways I simply do not. The result was a better piece than I could have produced on my own, and an audience that would never have found this newsletter otherwise.
March: The ToxSec Collaboration
March brought a second partnership that hit differently: a collaboration with ToxSec from the ToxSec newsletter.
ToxSec published “Nobody Knows What to Call This Job Yet” on his side (read it here). I published the companion piece, “What Each AI Security Role Actually Expects From You” (on my side), which used the job market analysis from our discussions to map exactly what skills and mindset shifts each AI security role actually demands from practitioners.
That post pulled 125 views, 5 reactions, a comment thread, and 4 signups in the first 24 hours: the strongest first-day engagement of any March post. More importantly, it was the piece with the highest reaction count of any Q1 post I actually emailed to the list.
ToxSec’s work sits at the intersection of frontier AI and applied security thinking in a way that is genuinely rare. If you are here because you care about where AI security is heading as a profession, you should be reading both. Go subscribe to ToxSec at toxsec.substack.com, and keep reading this one. :)
The Governance Thread
The final weeks of Q1 brought a governance series aimed at giving AI security practitioners a clear picture of the actual regulatory landscape: not policy summaries for lawyers, but a practical map of how the frameworks being assembled around AI systems should shape the way security people think and operate. “The Three-Layer Compliance Stack“ (March 17), “NIST, ISO 42001 and IEEE“ (March 19), “EU AI Act High-Risk Classification“ (March 24), and “International AI Governance: OECD, G7 and Bletchley Standards“ (March 26) cover the terrain from technical standards to international coordination, with a practitioner lens throughout. Open rates on that thread have been consistent at 28% to 31%, which tells me the security audience here cares about the regulatory layer too.
What’s Coming in Q2
The governance thread is not the main event for Q2.
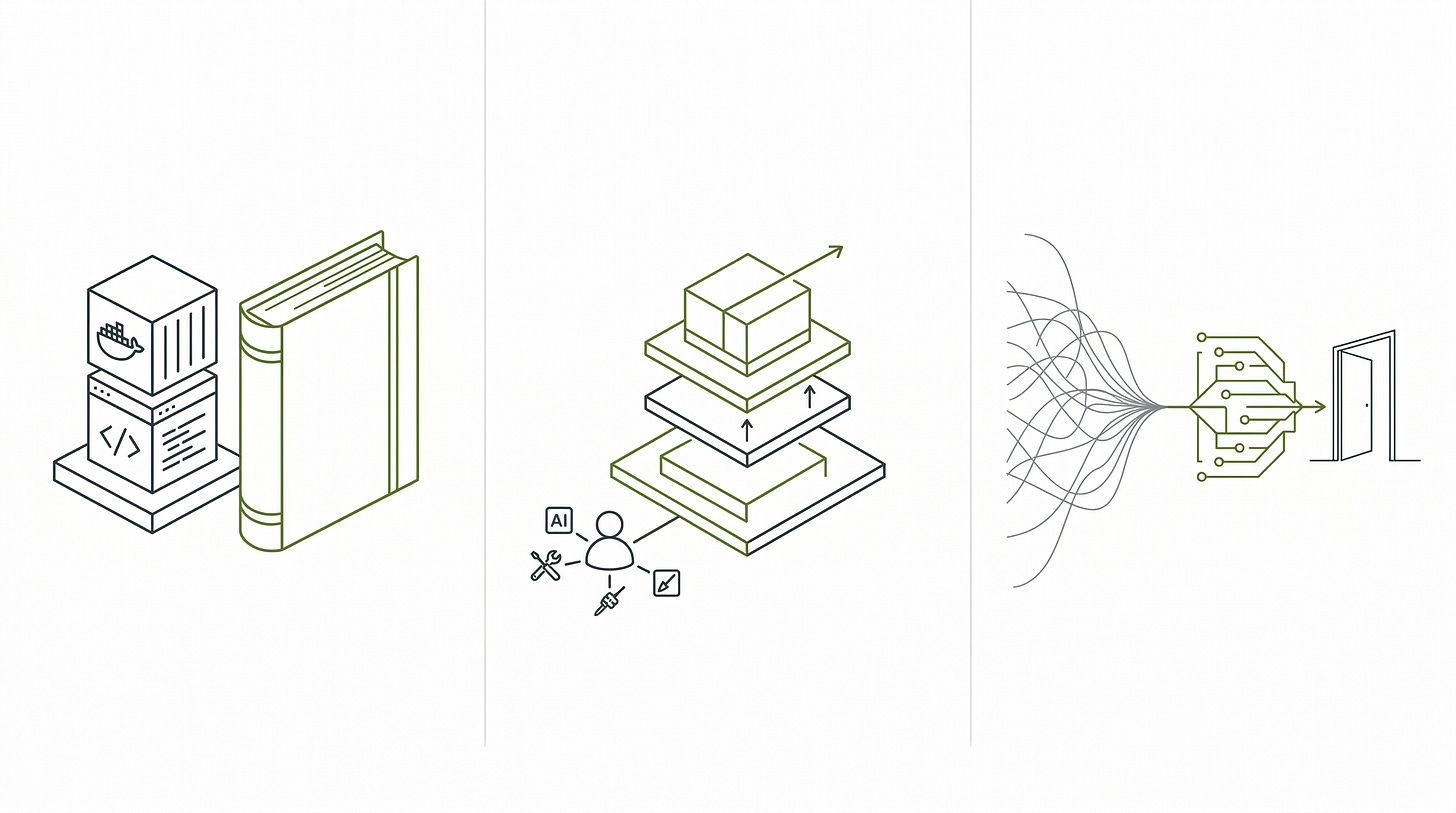
That is the Agentic AI Security Stack: the full guide that every individual post since October has been building toward. Threat model, credential architecture, isolation and sandboxing, egress control, human-in-the-loop as a security control, memory and RAG security, orchestration controls, and the rest, assembled into a single reference document covering implementation patterns, decision frameworks, and the complete kill chain that threads all twelve layers together.
I called it a guide in the February preview. That was optimistic about its size. It is now over 200 pages and is, by any honest measure, a book. The preview post made a promise; Q2 is when it ships. And because I believe this knowledge should reach everyone who needs it, it will be freely available.
Beyond the book, Q2 will also bring something that has been missing from the security content so far: working code. If you followed the Glass Citadel series, you know what that looks like: Docker stacks, reference implementations, things you can actually run. The security layer articles have been architecture and reasoning. Q2 adds the implementations. Credential architecture, isolation patterns, egress controls: the same layers we have been mapping out, but now with code you can fork and adapt. This body of theory has been laid out. Now it is time to start building on top of it.
A Genuine Thank You
Most of the growth this quarter came from two things: consistency and generosity from collaborators.
I published twice a week without exception. That discipline matters more than any individual piece. But the actual inflection points, the posts that brought new readers in rather than just keeping existing ones engaged, were both tied to people who trusted me enough to attach their name to a joint effort.
Wyndo and ToxSec: I am genuinely grateful. The work is better because you were involved in it.
If you write about AI or AI security and think there is a natural overlap with what this newsletter covers, I would love to hear from you. The two collaborations this quarter showed me that the right partnership makes both pieces better than either would have been alone. That is a formula worth repeating.
One more post lands on March 31 before this recap publishes: “LiteLLM Attack Wasn’t an AI Security Problem and Supply Chain Attackers Don’t Need to Understand AI to Own Your AI Stack,” a reflection on last week’s LiteLLM incident. Then Q2 begins.
To everyone who subscribed this quarter: welcome. To everyone who will find this newsletter in Q2 and beyond: welcome in advance. There is a lot more coming.
One last thing worth saying out loud. This newsletter started as a generalist AI exploration and has landed squarely in AI security. That is not a pivot; it is just how the journey works. You learn something deeply enough to see what needs to be secured, and then you secure it. The next big thing is always waiting on the other side of the current one. That is what keeps this interesting, and it is what keeps me writing.
I genuinely believe the future of tech work belongs to people who can do this repeatedly: build a real spike of depth, connect it to the next one, and keep the broad foundation strong enough to see across domains. The T-shaped professional still has real value, and always will. But the M-shape is what the next decade of AI demands: multiple spikes of genuine expertise, connected by the same intellectual curiosity that produced each of them. The people who will matter most are not the ones who mastered one thing early and stopped. They are the ones who treat depth as a habit. That is the journey this newsletter is here to document and, wherever possible, to accelerate for the people reading it.
Peace. Stay curious! End of transmission.



Awesome report, Fernando! :)
Thanks for contributing to AI Maker. Your post clearly shows that you know what you’re talking about and that you care deeply about the security issues with OpenClaw, by helping people become aware of them and reduce the risk of security leaks.
I love this quarter’s report, I might need to consider following the same approach!